This blog answers the question of which email protocol uses port 143 for unsecured communication? First of all, it discusses the ports for email protocols. Then it talks about the mail transfer protocol, SMTP, and its port. It then talks about the next layer protocol, the internet message access protocol, imps, and its port. A brief overview of imps and imap3 is given. Then it moves towards the third layer protocol, the mailbox access protocol, mbox, and its port.
Table of Contents
ToggleDetails About Which Email Protocol Uses Port 143 For Unsecured Communication?
Emails are not very secure and emails that are unsecured are becoming even less secure in today’s world. Email protocol is one of the important aspects of running an email service. This blog will look at the different protocols that are used to send emails. The most common one is SMTP (Simple Mail Transfer Protocol) which runs on port 25. There are others such as POP3, IMAP, and SMTP. This blog will look into the working of each of these email protocols and will also focus on the one in which Email protocol uses port 143 for unsecured communication.
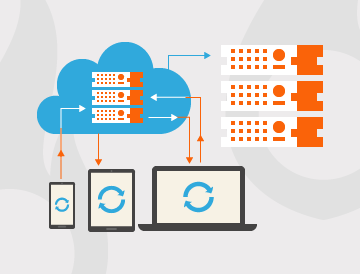
Different Transfer Protocol System
Email communication is the most commonly used protocol to communicate. There are different protocols used by different email clients to communicate. The most commonly used protocol is SMTP. SMTP stands for Simple Mail Transfer Protocol. In this blog, we will talk about the unsecured SMTP which is also used to communicate but it uses a different port and protocol.
Simple Mail Transfer Protocol
SMTP (Simple Mail Transfer Protocol) is used to send emails between servers. Port 25, which is the default port for sending emails, can only be used for secure communication. However, port 143 can be used for unsecured communication. SMTP or Simple Mail Transfer Protocol is a network protocol used by computers to transfer electronic mail messages from one system to another now we see which email protocol uses port 143 for unsecured communication that is defined do Before a message can be successfully transferred from the sender’s system to the recipient’s system, the message needs to pass through intermediate systems that connect the two systems.